As ransomware groups evolve, their methods of operation, encryption techniques, and evasion tactics continues to become more sophisticated. ransomMDR is built with the foresight and adaptability to evolve beyond ransomware and advanced threats.
Customers are struggling with ransomware despite having a robust security stack and endpoint protection being more advanced than ever.
The current generation of endpoint protection is outmatched and endpoint detection and response platforms and are too slow to stop ransomware.
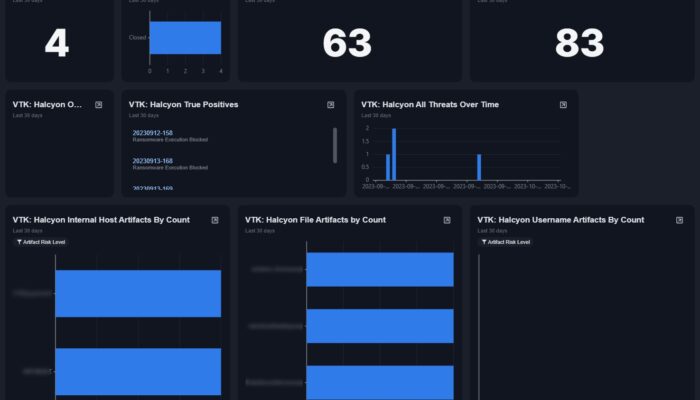
ransomMDR uses Vertek’s security services to keep your systems safe. Vertek monitors security and event logs and filters out false alarms to help our security analysts focus on real threats.
Current technologies cover a broad range of basic threat protection, but ransomware behaves differently than run of-the-mill malware.
Two Big Problems with EPP and EDR
``In the realm of cybersecurity, the adversaries are relentless, and the landscape is
perpetually shifting. Our alliance with Vertek is not just strategic; it's essential. By
melding Halcyon's state-of-the-art anti-ransomware capabilities with Vertek's
profound expertise in managed detection and response, we're not merely
addressing the threats of today. We're anticipating the challenges of tomorrow,
ensuring that businesses have a proactive, agile, and resilient defense in an era
where cyber risks are omnipresent.``
