Purpose-Built Managed XDR: Add Cost-Effective Breach Defense with cyber360 MXDR
Extended Detection and Response (XDR) is a unified cybersecurity platform that ingests data and events from key security tools you may already own. Add Vertek’s 24x7, 100% US-based SOC and response team, and you’ve got Managed Extended Detection and Response (MXDR) guarding your business from the ever-evolving threat landscape.
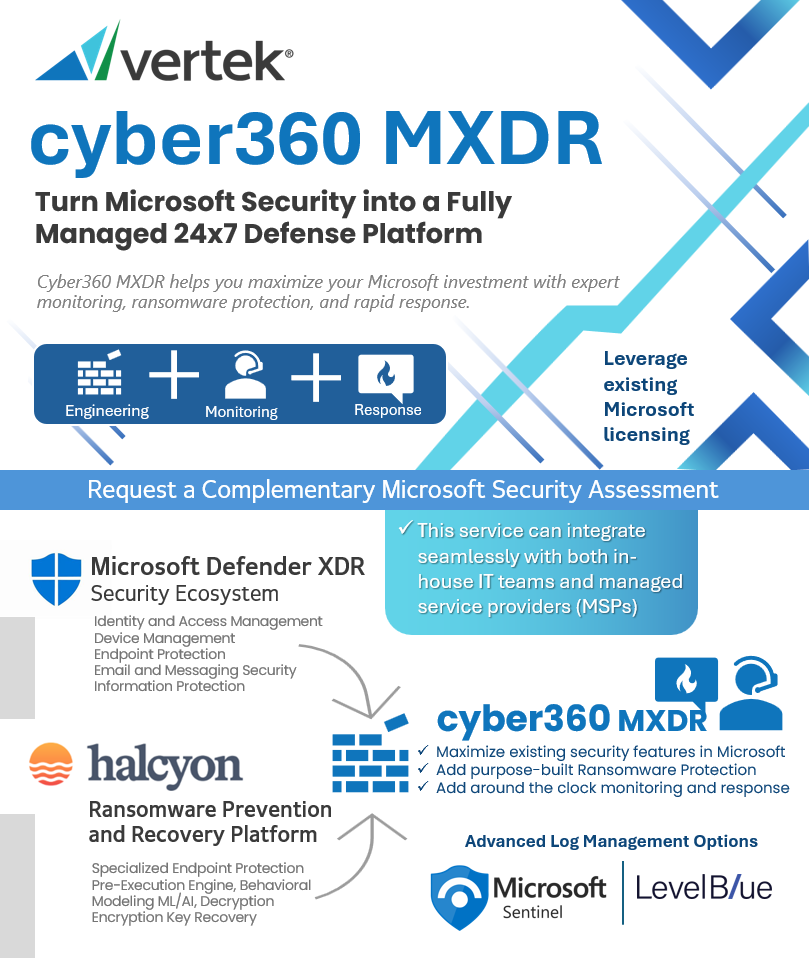
We've designed our cyber360 MXDR service to be both a smart financial decision and a powerful tactical advantage in stopping data breaches.
Under the Hood: Our OEM XDR Technology

Monitor and Take Action on Multiple Security Products
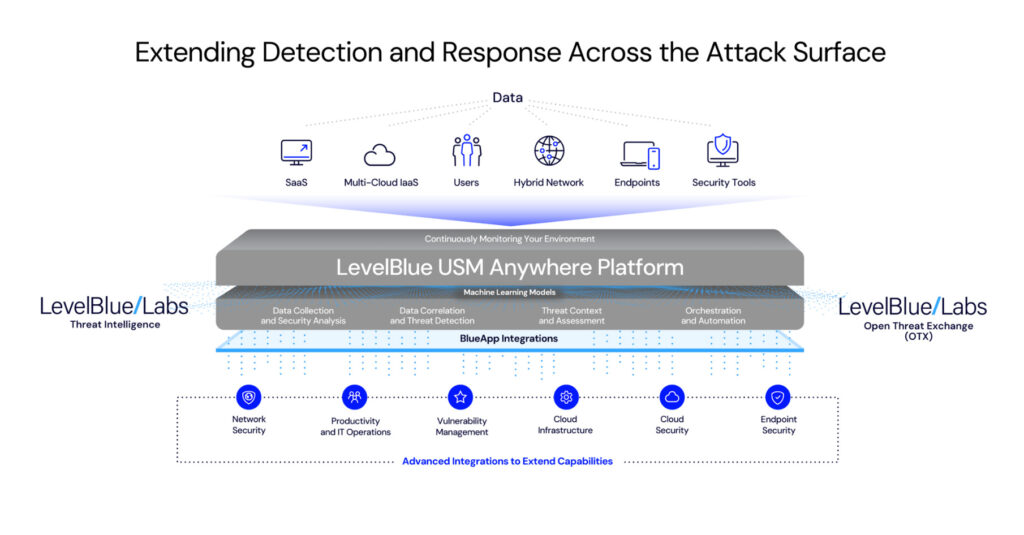
Fully managed and licensed by Vertek, LevelBlue's USM Anywhere Platform is an OpenXDR cloud-based security monitoring solution that integrates essential capabilities for effective threat detection and incident response across cloud, hybrid cloud, and on-premises environments, providing a unified, single-pane-of-glass experience.
Vertek Security Analysts are AVSE certified. As a LevelBlue advisory MSSP with advanced product experience and thousands of custom directives and alarms, Vertek excels in monitoring and responding to security alarms across a wide range of security products and complex environments.

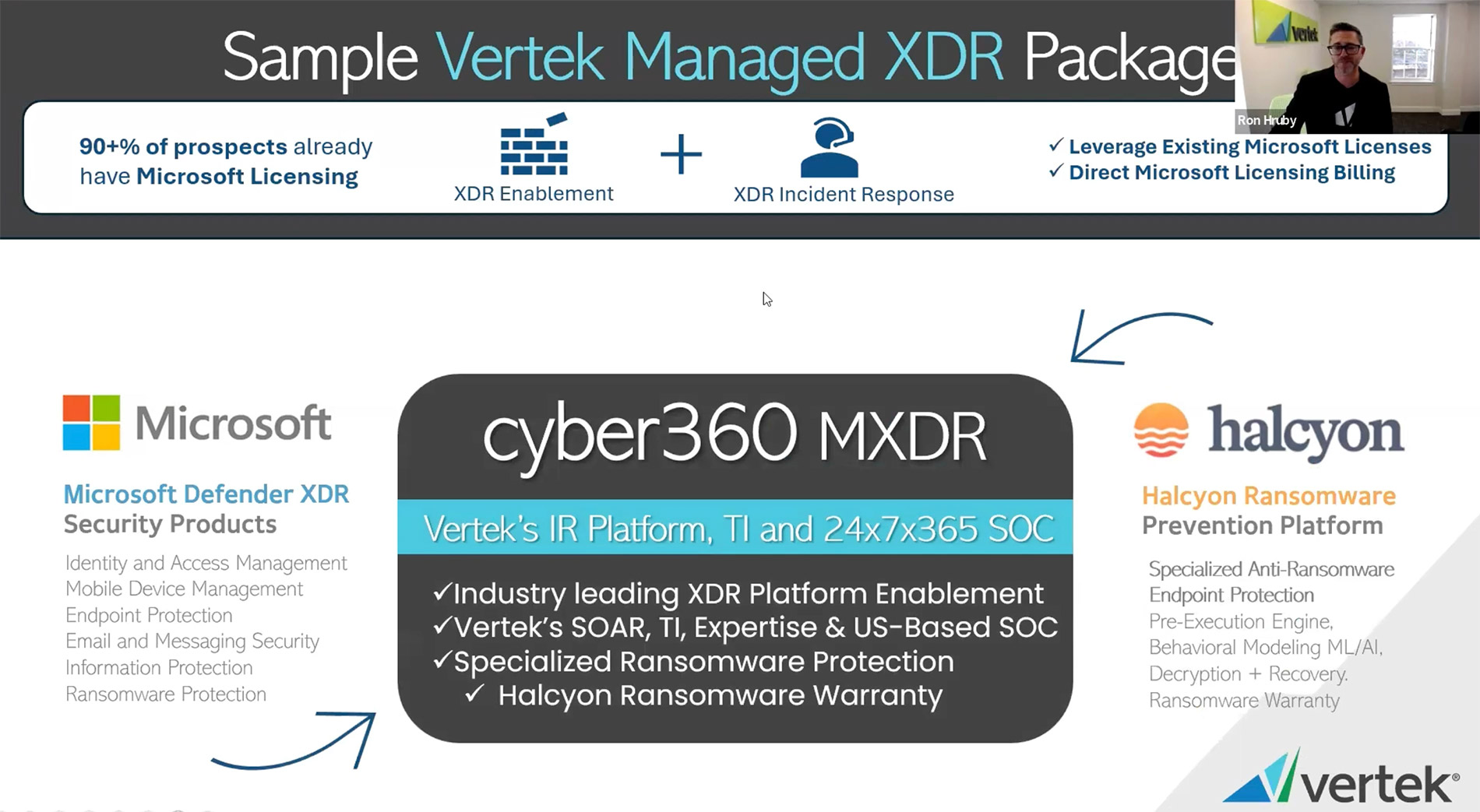
Deploy, Manage and Monitor Microsoft Security Products
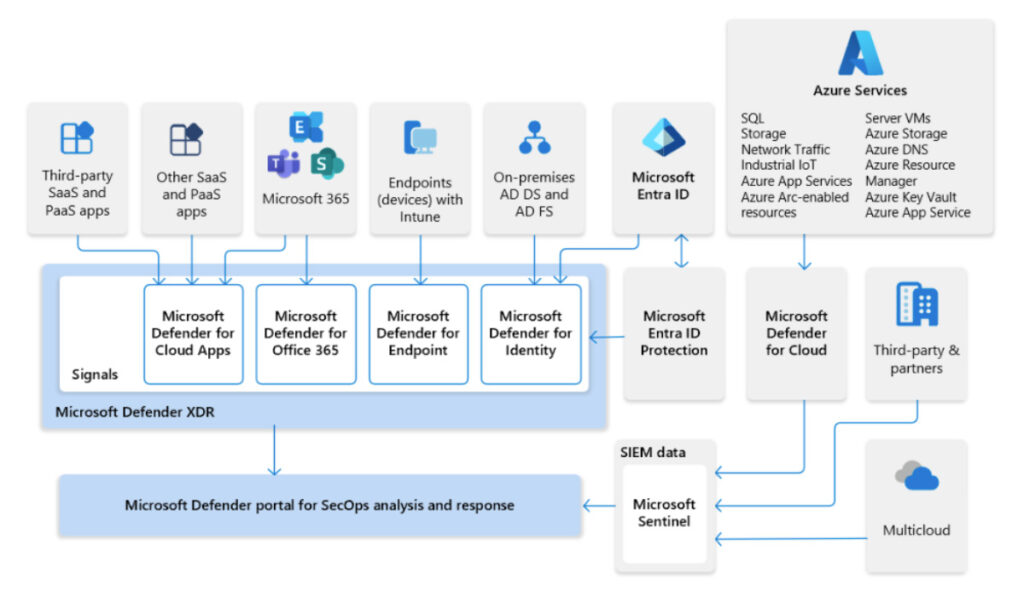
Vertek co-manages Microsoft Defender XDR, a comprehensive enterprise defense suite that integrates detection, prevention, investigation, and response across various platforms to protect against sophisticated attacks.
As a Microsoft Cloud Service Provider (CSP) with certified expertise in Microsoft security products and licensing, Vertek configures and optimizes Microsoft licensed security products to ensure controls are deployed to our recommended standards and alerts are set up for incident response triage.

24x7 Security Alarm Triage and Incident Response
All Managed Services are backed by Vertek's US-Based Security Operations Center (SOC).

How cyber360 MXDR Works
If a virus tries to infect your computers, MXDR will quickly detect it and stop it before it can spread.
If someone tries to hack into your email or cloud applications, MXDR will sound the alarm and prevent them from accessing your sensitive data, revoking user sessions.
MXDR works seamlessly with your existing tools, making it easy to manage and providing peace of mind knowing your data is protected.
Why Choose Vertek Managed Extended Detection & Response (MXDR)?
Vertek’s cyber360 MXDR solution is purpose-built for rapid deployment, enabling organizations to quickly strengthen their security posture. With flexible, scalable subscription pricing, clients can consolidate multiple security tools into a single, integrated platform—streamlining operations, accelerating threat detection, and simplifying response.
Ready to elevate your cybersecurity strategy? Partner with Vertek and experience a smarter, more efficient approach to threat protection.
Related Services
Explore our expansive portfolio of cybersecurity services, each engineered to fortify defenses, streamline operations, and empower your organization’s resilience.
Tell Us More About What Vertek Can Do For You.
Thank you for reaching out to Vertek. We strive to respond to all general inquiries within two business days.
Related Resources & Trends
Understanding the Differences Between EDR, MDR, and XDR

Got Questions? We Have Answers!
Get started by reaching out to our awesome support team today!