
Transform Security Data Into Actionable Security Insights with threatMDR
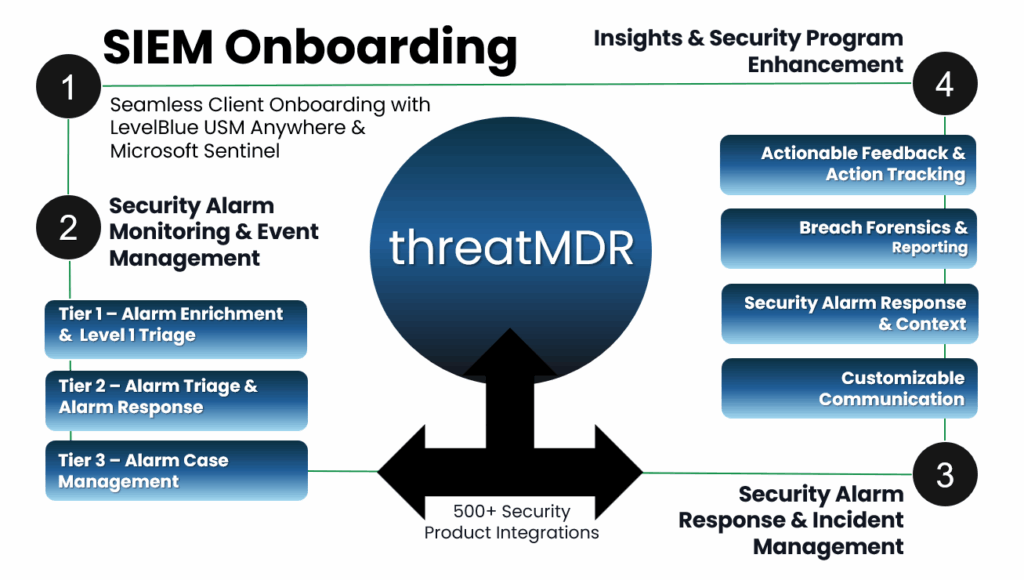
Energize your security information event management with threatMDR—offering 24x7 SIEM configuration and monitoring, real-time threat intelligence, and expert support to defeat data breaches and alleviate security alarm fatigue.
Our team has extensive expertise with LevelBlue and Microsoft SIEM products, validated by our team and trusted to deliver optimal outcomes under Vertek's management.
Managed LevelBlue

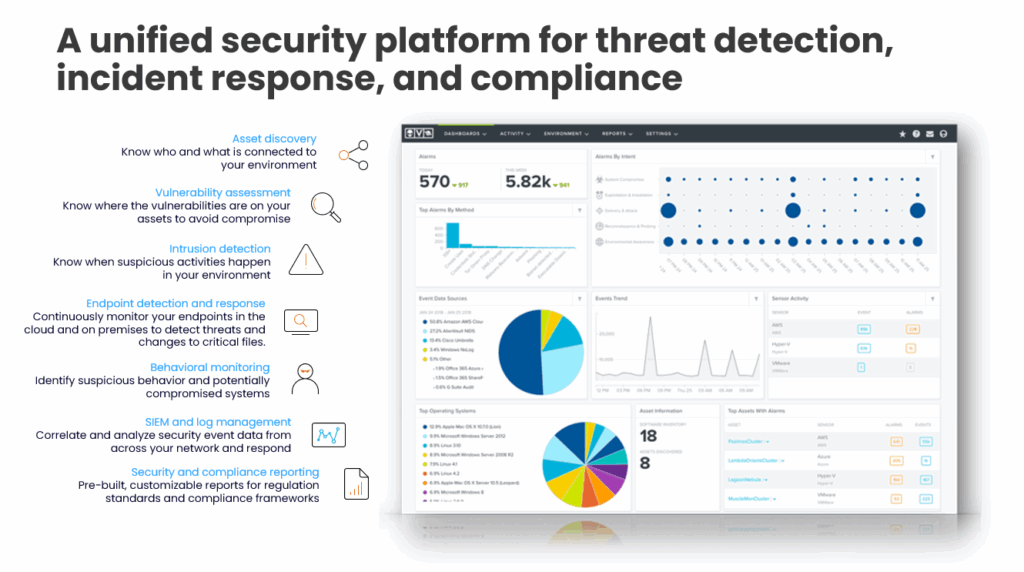
LevelBlue's USM Anywhere™ SIEM capabilities perform strong in complex, non-Microsoft native environments where Network Detection and Response (NDR), vulnerability scanning and IoT monitoring are critical. Vertek fully manages LevelBlue, including licensing, to deliver seamless and effective security information event management platform backed by our security operations center.
15-day, 30-day, 90-day and 180-day active log retention available with unlimited cold storage.
Managed Sentinel

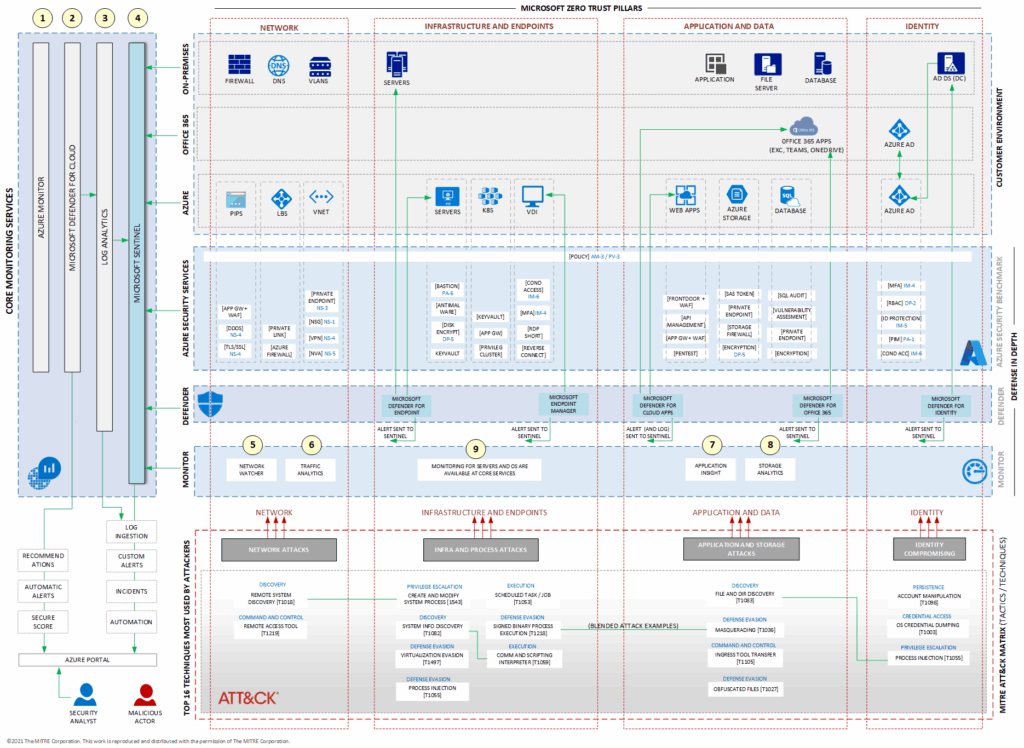
Microsoft Sentinel is a scalable, cloud-native security information and event management (SIEM) platform that delivers an intelligent and comprehensive solution for SIEM- Intergrated into Azure and Microsoft Defender XDR security services.
Map threats to your IT environment by establishing a robust defense with Azure Security services. Enhance this protection by integrating Microsoft Defender XDR security services into Microsoft Sentinel for a comprehensive, multi-layered security strategy:

Service Lifecycle
How do Vertek's SIEM Services Differ from a Crowded Field?
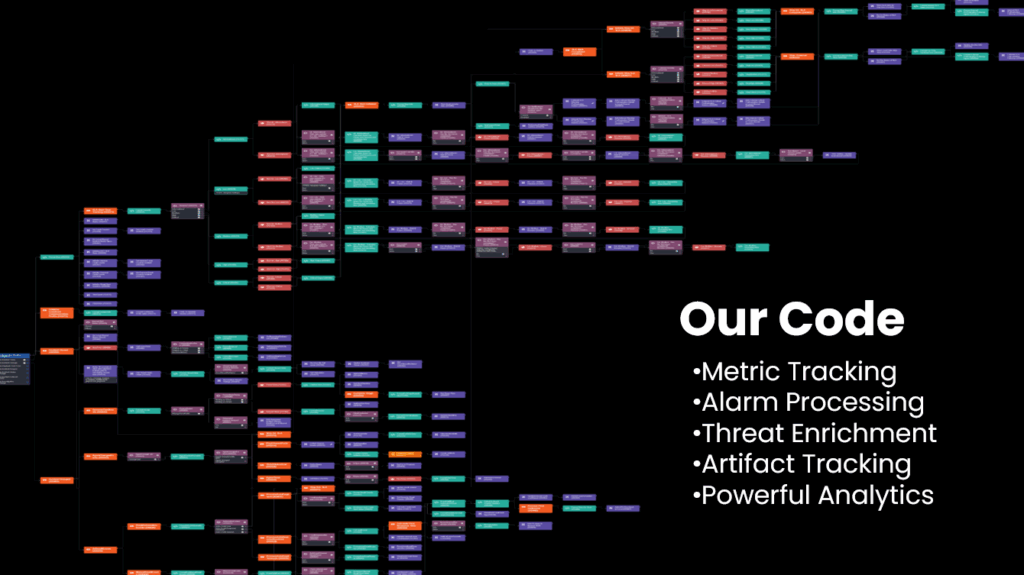
Playbooks and Automation: Vertek's SIEM services are backed by advanced threat intelligence, proprietary playbooks and automation to streamline incident response. This ensures rapid and efficient handling of security events, minimizing downtime and reducing the burden on IT teams.
Custom Directives and Alarms: Vertek provides tailored directives and alarms, along with proprietary checks for both Microsoft Sentinel and LevelBlue. These custom solutions enhance threat detection and response, ensuring that your security measures are precisely aligned with your organization's needs.
Expert Customization and Support: Our team of certified security engineers provides tailored SIEM solutions and ongoing support, ensuring optimal performance and actionable insights. This personalized service meets the unique needs of each client.
Why Choose Vertek Managed SIEM?
Vertek’s Managed SIEM services are designed to help organizations cut through the noise, reduce alert fatigue, and turn security data into actionable insights—without the overhead of managing complex tools in-house. Backed by our 24x7 US-based SOC and deep expertise in Microsoft Sentinel and LevelBlue, we deliver a smarter, more efficient approach to SIEM.
Related Services
Explore our expansive portfolio of cybersecurity services, each engineered to fortify defenses, streamline operations, and empower your organization’s resilience.
Tell Us More About What Vertek Can Do For You.
Take the first step toward robust security by requesting your free security assessment today. Complete our quick form to unlock tailored insights that safeguard your business.
Related Resources & Trends
No posts

Got Questions? We Have Answers!
Get started by reaching out to our awesome support team today!







