Vertek’s OTX Public and Private Pulses provide a summary of the threat, some information regarding the software targeted, and the related indicators of compromise (IoC) that can be used to detect threats. Vertek utilizes several methods and various tools to obtain IoCs we feed into our Pulses. Please test accordingly and use at your own discretion. IoCs types include IP addresses Domains Hostnames (subdomains) Email URL URI File Hashes: MD5, SHA1, SHA256, PEHASH, IMPHASH......
Read More
Latest Locky Variant Encrypts with Ykcol Extension – IoCs and OTX
As you can see, our labs team is still seeing Locky is being distributed in a lot of malspam...
Read MoreWebsite Ransomware Trending Now
Vertek’s security operations team has noticed website ransomware is starting to pick up steam with recent variants of AwesomeWare,...
Read MoreLocky Now Pushing .Lukitus Variant – IoCs and OTX
Locky is being distributed at mass scale via phishing and spam email attacks by two major botnets; Necurs and...
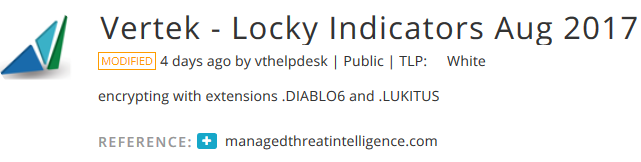
Read MoreLocky DIABLO6 Ransomware Campaign Launched – IoCs and OTX
Locky IoCs extracted by our security operations center. Public Pulse | TLP: White | encrypts with extension .DIABLO6 OTX...
Read MoreGlobe Imposter Ransomware – IoCs and OTX
Glob Imposter IoCs extracted by our security operations center. Public Pulse | TLP: White | Encrypt filesystem with extension...
Read MoreAutomated PhishTank IoCs and OTX feed – Verified/Online Banking Phishing URLs
This is an automated process that is updated hourly by the Vertek MTI Labs Team. We pull all active/online...
Read MoreAutomated PhishTank IoCs and OTX feed – Verified/Online GoogleDocs Phishing URLs
This is an automated process that is updated hourly by the Vertek MTI Labs Team. We pull all active/online...
Read More