Boom, and just like that you are compromised. The “Left of Boom” is the timeframe beforehand, the preventative approach. While much of the industry attention has been on the ability to react quickly and contain intrusions, or “Right of Boom,” it is the prioritization of detecting and responding to a threat before it compromises a system where a truly comprehensive and effective approach lies. Detecting attacks early can make a difference between facing an......
Read More
The Top Cybersecurity Predictions for 2024
In 2024, companies will lose an estimated 10.5 trillion dollars due to cyberattacks. This could be daunting to small...
Read MoreThe Importance of Managed Detection and Response for Small and Medium-Sized Businesses: A Financial and Security Analysis
Introduction: In today’s digital landscape, small and medium-sized businesses (SMBs) face an increasing number of sophisticated cyber threats that...
Read MoreProxyNotShell: Zero-Day Vulnerabilities in Microsoft Exchange Server
Summary: Back at the start of August 2022, members of GTSC came across an attack where Microsoft Exchange was...
Read MoreFollina: Microsoft Office Zero Day Vulnerability
On 5/27/22 security research team, Nao_sec identified a malicious Word document in the wild, that appeared to be leveraging...
Read MoreLog4Shell Vulnerability
Summary: On Dec. 9, 2021, Proof of Concept exploitation code for the remote code execution (RCE) vulnerability (CVE-2021-44228) in...
Read MoreThe Top 4 Reasons Why Organizations Like Yours Leverage Vertek for Cybersecurity
Today’s cyber criminals have learned to capitalize on vulnerabilities created by hybrid workforces and understaffed IT and security departments....
Read MoreCritical PrintNightmare Vulnerability Patches
Summary: Window’s Print Spooler is run by default on all supported Windows operating system versions as it is a...
Read MoreKaseya VSA Attack Delivers REvil Ransomware
Summary: On 07/02/2021, Kaseya disclosed an ongoing attack exploiting on-premise Kaseya VSA servers, along with an advisory to their...
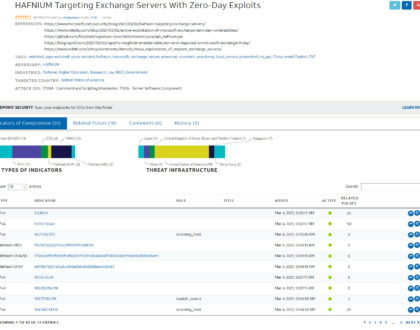
Read MoreHAFNIUM: Exchange Zero Days Actively Exploited by APT Group
Summary: On 3/2/21, security researchers at Volexity released a blog with their findings following their discovery of four new...
Read More